Container vulnerability scanning
Identify more vulnerabilities and accelerate remediation.
Protect cloud-native workloads with continuous vulnerability scanning for container images.
Benefits
What is container vulnerability scanning?
The purpose of a software container vulnerability scan is to harden container images by identifying malware, secrets, security risks, and vulnerabilities in the software components. This can happen in CI/CD pipelines, registries, and Kubernetes platforms.
Automate container scanning.
Leverage comprehensive APIs and a CLI tool to automate image scanning for development environments, CI/CD pipelines, registries, or runtime environments.
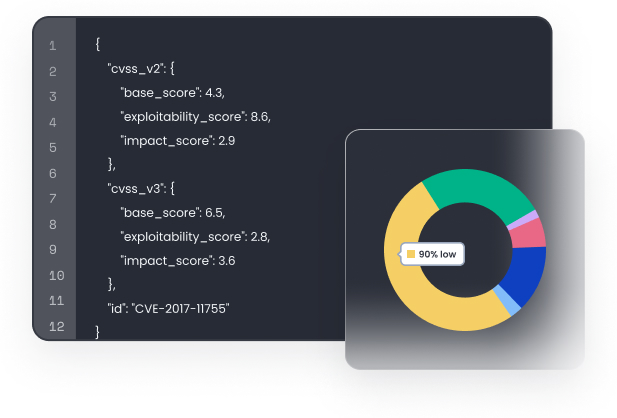
Fewer false positives.
Accelerate software delivery with curated vulnerability feeds, optimized vulnerability matching, and a unique feedback loop that reduces false positives and false negatives.
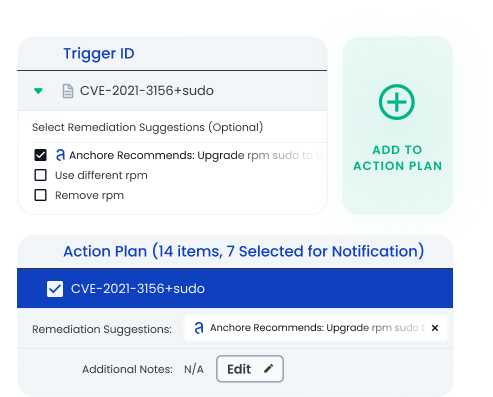
Quicker, easier remediation.
View, manage, and fix vulnerabilities and security issues in container images quickly with automated remediation recommendations and workflows.
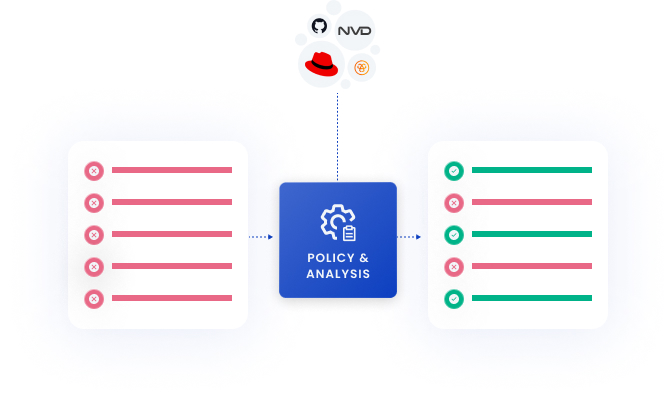
How Container Vulnerability Scanning works.
Inspect and secure workloads across the entire software supply chain
Easily integrate across your toolchain.




















Speak with our security experts
Learn how Anchore’s SBOM-powered platform can help secure your software supply chain.