How Anchore’s DevSecOps solutions help
From source to deployment, the Anchore platform protects your organization at every step of the way. Want to learn more about DevSecOps and its role in software supply chain security? Explore Anchore’s platform with a 15-day free trial.
What you get with Anchore
Anchore provides DevSecOps integrations for your existing toolchain. Whether looking for known vulnerabilities, secrets, malware, or insecure configurations, Anchore Enterprise searches continuously for issues and enables security teams to triage, remediate, and report more efficiently.
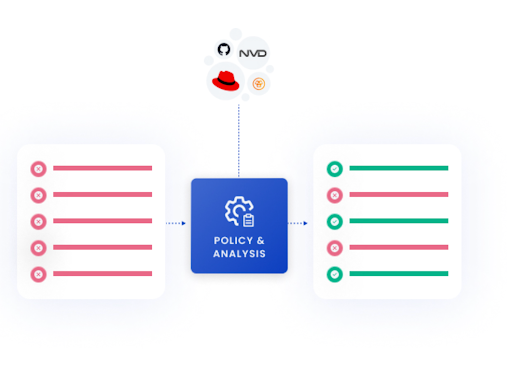
Continuous vulnerability scanning
Automate vulnerability scans at each step in the development lifecycle, including source code repositories, CI/CD pipelines, container registries, and Kubernetes platforms. Identify vulnerabilities, malware, secrets, and security risks.
Explore container vulnerability scanning here.


Frictionless developer experience
100% API coverage and fully-documented APIs enable developers to work seamlessly in the tools they already use. Automate scanning in source code repos, CI/CD pipelines or container registries through native integrations. Streamline remediation of issues with notifications through GitHub, JIRA, Slack, and more.
Track SBOM drift
Detect SBOM drift in the build process to uncover unexpected dependencies, malicious efforts to infiltrate builds, and inadvertent errors. Alert security staff to changes in SBOMs so they can be assessed for risks or malicious activity.
Discover SBOM management solutions.
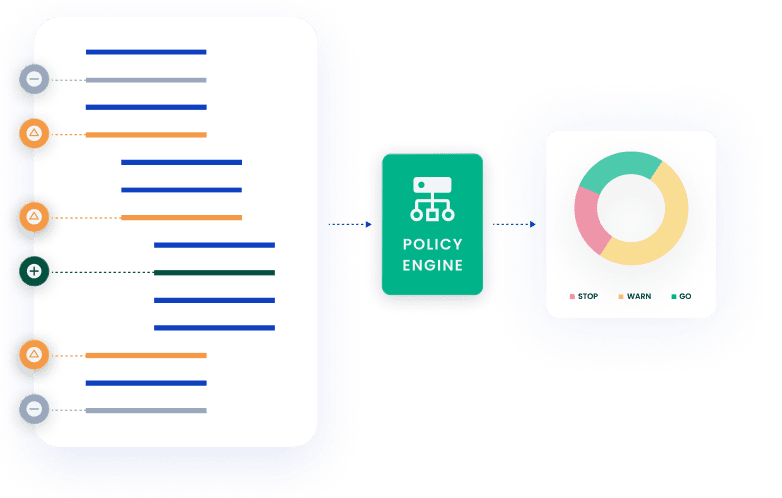
Fewer false positives
Optimize development velocity with an unparalleled signal-to-noise ratio. Get fewer false positives with vulnerability results that are pinpointed to a specific distro. Use flexible policies to prioritize based on severity or availability of a fix. Provide “corrections” and “hints” that improve results going forward. Add vulnerabilities to allowlists to prevent ongoing alerts.
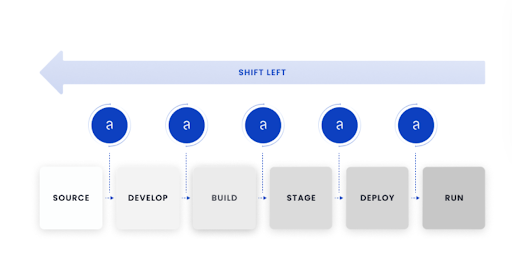
Shift security left
Find and fix vulnerabilities earlier to keep development moving. Start automated scanning in the development and build phases to uncover new dependencies and vulnerabilities. Continue scanning against container registries and pre-deployment to ensure components remain secure.
See the product here.
Why Anchore
Led by a team with extensive experience in automation and cloud computing, Anchore was founded to enable efficient security workflows at scale. Rather than require changes to tools or processes, Anchore Enterprise integrates with your existing environment to check the security posture of your applications and surface the most critical issues at every stage of development.
Anchore Enterprise enables a “shift left” approach which ensures issues are identified as early as possible and flagged with the appropriate teams. As software moves from CI/CD to Runtime, Anchore Enterprise catalogs the components at every stage and ensures that insecure software is never put into production.