Federal Software Compliance
Enforce federal software supply chain security compliance
Automate policy enforcement, compliance and reporting for the U.S. Department of Defense DISA STIGs, Iron Bank, FedRamp, NIST and CISA policies.
Benefits
Comply with Federal Security Standards
The federal policy library includes new controls such as inspecting for malware and secrets, scanning for known vulnerabilities, and generating software bill of materials (SBOM).
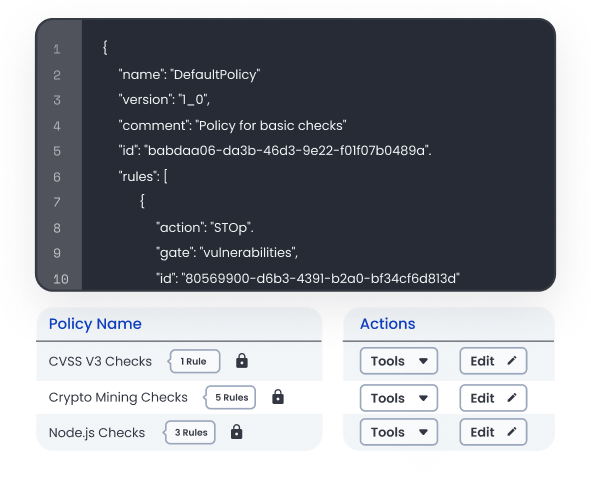
Automate Policy Enforcement
Alert application developers or security engineers to failures as software is being developed and built instead of before your compliance audit.

Streamline Reporting
Anchore’s reporting capabilities enable security teams to demonstrate their level of compliance as part of formal reporting requirements.
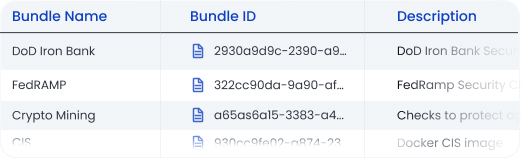
The Anchore policy library consists of controls and policies to help organizations reach compliance.
NIST Special Publication 800-190
Application Container Security Guide
NIST Special Publication 800-53 Revision 5
Security and Privacy Controls for Information Systems and Organizations
NIST Special Publication 800-218
Secure Software Development Framework (SSDF) Version 1.1: Recommendations for Mitigating the Risk of Software Vulnerabilities
U.S. Department of Defense
Defense Information Systems Agency (DISA) STIG Guidelines
U.S. Department of Defense
Defense Information Systems Agency (DISA) Container Image Creation and Deployment Guide
FedRamp
Vulnerability Scanning Requirements for Containers
CISA
Known Exploited Vulnerabilities Catalog
Platform One Iron Bank
Related resources.
Speak with our security experts
Learn how Anchore’s SBOM-powered platform can help secure your software supply chain.