Container Compliance
Enforce software container compliance.
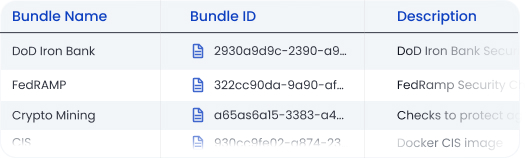
Prove compliance for CIS Benchmarks, NIST, FedRAMP, DISA STIGs, CISA Known Exploited Vulnerabilities and more.
Benefits
Comply with Standards
Get started quickly with predefined policy packs to ease compliance with standards including NIST, CIS, HIPAA, PCI, FedRAMP, DISA STIGs, CISA Known Exploited Vulnerabilities and more.
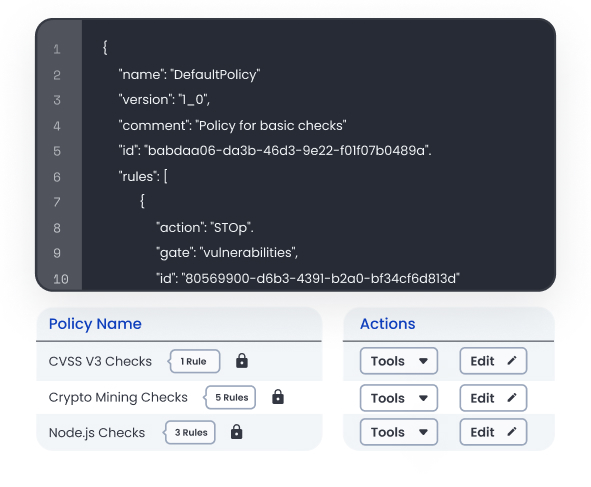
Easy to Customize.
Meet internal and external standards with policy-based compliance controls customized to your organization’s unique requirements.
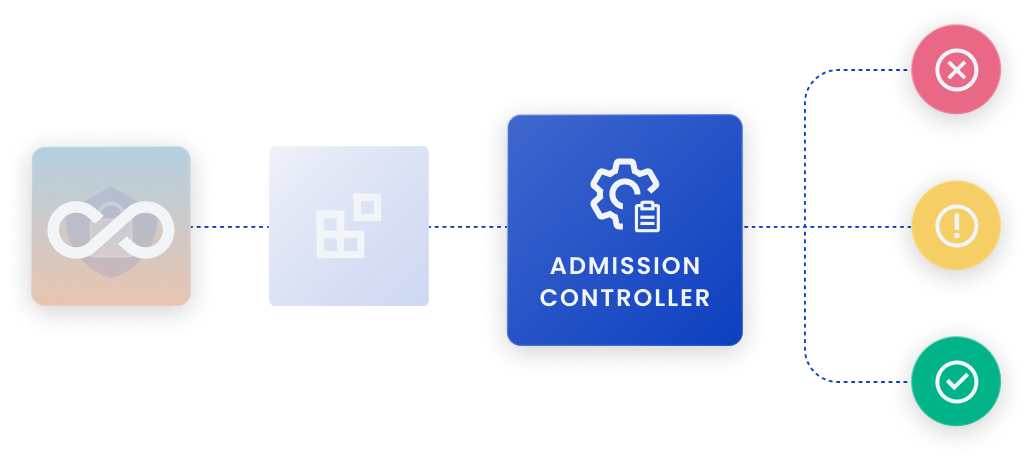
Empower DevOps.
Embed fully-automated compliance checks into your CI/CD pipeline. Receive compliance alerts through the developer tools you already use.
Comprehensive Container Compliance Tools.
NIST
Leverage automated policies to comply with NIST container security standards detailed in NIST SP 800-190.
CIS Docker
Streamline compliance with Center for Internet Security (CIS) Docker Benchmarks with an out-of-the-box CIS Policy Pack.
DISA STIG
Fully automate Software Technical Integration Guide (STIG) checks for containers running in a Kubernetes cluster and give security teams a single dashboard to report on DISA STIG compliance issues.
Related resources.
Speak with our security experts
Learn how Anchore’s SBOM-powered platform can help secure your software supply chain.